Cloud & Application Security
New CrowdResponse Modules
CrowdStrike is excited to bring new capabilities to platform engineering and operations teams that manage hybrid cloud infrastructure, including on Red Hat Enterprise Linux and Red Hat OpenShift. Most[…]
Three Ways to Enhance Your Cloud Security with External Attack Surface Management
The massive increase in cloud adoption has driven adversaries to focus their efforts on cloud environments — a shift that led to cloud intrusions increasing by 75% in 2023, emphasizing the need for st[…]
CrowdStrike Cloud Security Defines the Future of an Evolving Market
Today’s businesses are building their future in the cloud. They rely on cloud infrastructure and services to operate, develop new products and deliver greater value to their customers. The cloud is th[…]
5 Best Practices to Secure AWS Resources
Organizations are increasingly turning to cloud computing for IT agility, resilience and scalability. Amazon Web Services (AWS) stands at the forefront of this digital transformation, offering a robus[…]
Porter Airlines Consolidates Its Cloud, Identity and Endpoint Security with CrowdStrike
As Porter Airlines scaled its business, it needed a unified cybersecurity platform to eliminate the challenges of juggling multiple cloud, identity and endpoint security products. Porter consolidated […]
Welcome to Fal.Con 2022: CrowdStrike Drives the Convergence of Security and Observability
The increase in cloud adoption has been met with a corresponding rise in cybersecurity threats. Cloud intrusions escalated by a staggering 75% in 2023, with cloud-conscious cases increasing by 110%. A[…]
5 Best Practices to Secure Azure Resources
Cloud computing has become the backbone for modern businesses due to its scalability, flexibility and cost-efficiency. As organizations choose cloud service providers to power their technological tran[…]
Welcome to Fal.Con 2023: CrowdStrike Ushers in the Future of Cybersecurity
In the ever-evolving landscape of cloud security, staying ahead of the curve is paramount. Today, we are announcing an exciting enhancement: CrowdStrike Falcon® Cloud Security now supports Google Kube[…]
Key Characteristics of Modern Fileless Attacks
As organizations shift their applications and operations to the cloud and increasingly drive revenues through software, cloud-native applications and APIs have emerged among the greatest areas of mode[…]
Hiding in Plain Sight: Remediating “Hidden” Malware with Real Time Response
As organizations move more of their business-critical applications to the cloud, adversaries are shifting their tactics accordingly. And within the cloud, it’s clear that cybercriminals are setting th[…]
CrowdStrike Debuts Counter Adversary Operations Team to Fight Faster and Smarter Adversaries as Identity-Focused Attacks Skyrocket
Azure cross-tenant synchronization (CTS) was made generally available on May 30, 2023, and introduced a new attack surface on Microsoft Entra ID (formerly Azure Active Directory) where attackers can m[…]
Architecture Drift: What It Is and How It Leads to Breaches
Cybercriminals work around the clock to discover new tactics to breach systems. Each time a digital ecosystem changes, it can introduce a weakness for a threat actor to quickly discover and exploit. A[…]
Many Paths, One Goal: Forging a Career in Cybersecurity
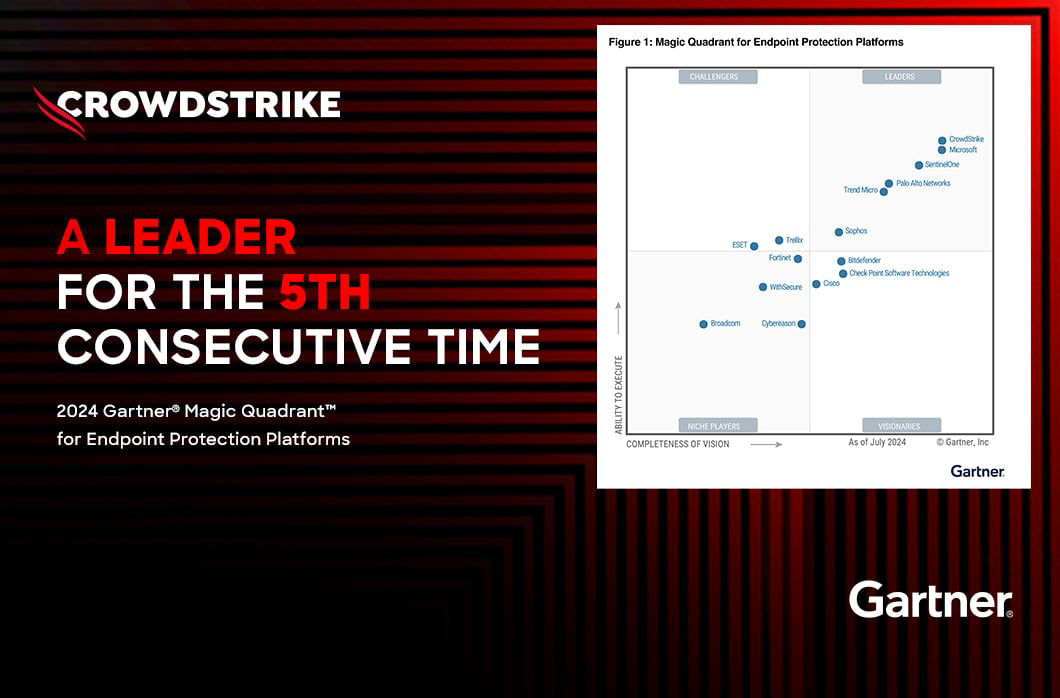
Today, we’re proud to announce that Forrester has named CrowdStrike a Leader in The Forrester Wave™: Cloud Workload Security, Q1 2024, stating “CrowdStrike shines in agentless CWP and container runtim[…]
Beyond Compliance: Secure Your Business in the Cloud with Falcon Cloud Security
Cloud infrastructure is subject to a wide variety of international, federal, state and local security regulations. Organizations must comply with these regulations or face the consequences. Due to the[…]
Development Cost of Porting TensorFlow Models to Pure Rust
According to the CrowdStrike 2023 Global Threat Report, there was a 95% increase in cloud exploits in 2022, with a three-fold increase in cases involving cloud-conscious threat actors. The cloud is ra[…]
RSAC 2022: CrowdStrike Delivers Protection that Powers Productivity
CrowdStrike is honored to be named Partner of the Year for several 2023 Geo and Global AWS Partner Awards at Amazon Web Services re:Invent 2023, where we are participating this year as a Diamond Spons[…]
The Difference Between Securing Custom-Developed vs. Commercial Off-the-Shelf Software
Modern applications are designed to process, use and store vast amounts of sensitive data. As adversaries seek to infiltrate these applications, IT and security teams must ensure the software they use[…]
Big Game Hunting TTPs Continue to Shift After DarkSide Pipeline Attack
CoreWeave is a specialized GPU cloud provider powering the AI revolution. It delivers the fastest and most consistent solutions for use cases that depend on GPU-accelerated workloads, including VFX, p[…]
EMBERSim: A Large-Scale Databank for Boosting Similarity Search in Malware Analysis
As organizations increasingly deploy business-critical workloads to managed cloud services, enforcing strong security practices needs to be a top priority. While many managed cloud service providers d[…]
CrowdStrike Discovers First-Ever Dero Cryptojacking Campaign Targeting Kubernetes
Two new privilege escalation CVEs, CVE-2023-2640 and CVE-2023-32629, have been discovered in the Ubuntu kernel OverlayFS module. The CVEs affect not only any Ubuntu hosts running with vulnerable kerne[…]
Security Guidance from the Front Lines of Cloud Incident Response
In our first-ever Cloud Threat Summit, CrowdStrike’s Senior Vice President of Intelligence and Senior Director of Consulting Services discussed the most common ways adversaries breach the cloud and th[…]
CrowdStrike Defines the Future of Cloud Security with One-Click XDR to Automatically Identify and Secure Unmanaged Cloud Assets
CrowdStrike is defining the future of cloud security by empowering customers to rapidly understand their cloud risk and to detect, prevent and remediate cloud-focused threats. Today we are announcing […]
CrowdStrike Falcon® Certified as Legacy AV Replacement
CrowdStrike is defining the future of cloud-native application protection platforms (CNAPP) with CrowdStrike Falcon® Cloud Security. As the industry’s most comprehensive agent-based and agentless clou[…]
Chaos in the Cloud: Rampant Cloud Activity Requires Modern Protection
Digital transformation isn’t only for the good guys. Adversaries are undergoing their own digital transformation to exploit modern IT infrastructures — a trend we’re seeing play out in real time as th[…]
3 Ways Visualization Improves Cloud Asset Management and Security
Public cloud services and cloud assets are agile and dynamic environments. Close oversight of these assets is a critical component of your asset management and security practices. While it’s important[…]
CrowdStrike and Verizon Form Partnership to Provide Integrated Solutions and Services to Customers
At AWS re:Invent 2022, CrowdStrike announced expanded service integrations with AWS to provide breach protection across your AWS environment, simplified infrastructure management and security consolid[…]
Securing PostgreSQL from Cryptojacking Campaigns in Kubernetes
PostgreSQL misconfiguration allows running shell commands on the underlying OS with the “COPY” SQL command and “pg_execute_server_program” role Kubernetes ingress can allow access to the PostgreSQL se[…]
Quadrant Knowledge Solutions Names CrowdStrike a Leader in the 2022 SPARK Matrix for Digital Threat Intelligence Management
CrowdStrike is excited to announce it has been recognized by Frost & Sullivan as a global leader in the inaugural 2022 Frost Radar™: Cloud-Native Application Protection Platform, 2022 analysis. We hav[…]
CrowdStrike Services Helps Organizations Prioritize Patching Vulnerabilities with CrowdStrike Falcon Spotlight
Enterprises are embracing cloud-native applications in the name of business agility. These applications enable developers to take advantage of the cloud’s scalability and flexibility, allow customers […]
Join CrowdStrike at AWS re:Invent 2020
Join us in Las Vegas Nov. 28-Dec. 2! CrowdStrike is a Diamond Sponsor at AWS re:Invent, and we’re looking forward to meeting with customers, partners and prospects to show how we’re protecting AWS env[…]
Building on the Shoulders of Giants: Combining TensorFlow and Rust
Cloud storage misconfigurations continue to become more prevalent and problematic for organizations as they expand their cloud infrastructure, driving the importance of technologies such as cloud secu[…]
CrowdStrike Integrated Intelligence and Deployment Automation Enhance New AWS Network Firewall
CrowdStrike has uncovered a new cryptojacking campaign targeting vulnerable Docker and Kubernetes infrastructure using an obscure domain from the payload, container escape attempt and anonymized “dog”[…]
Maze Ransomware Analysis and Protection
KubeCon + CloudNativeCon North America 2022 is happening next week, and we’re excited to showcase our industry leading cloud-native application protection platform (CNAPP) capabilities and observabili[…]
HIMSS and Beyond: What’s Next in Healthcare Security
As organizations continue to shift to multi-cloud environments and increasingly use cloud services for application development, new challenges emerge that require dramatic changes in the delivery and […]
CrowdStrike Is Proud to Sponsor the Mac Admins Foundation
Fourteen key cloud analytics for Azure and GCP cloud environments were identified and mapped as indicative of adversary behavior and serve as a blueprint for understanding and writing new cloud analyt[…]
CrowdStrike Falcon Platform Achieves Certification in AV-Comparatives' First Anti-Tampering Test
As organizations expand their cloud-native initiatives and increase their use of containers and Kubernetes in production, they face challenges regarding container security, monitoring, data management[…]
DirtyCred: Opening Pandora’s Box to Current and Future Container Escapes
What Is DirtyCred? DirtyCred is a new Linux kernel exploitation technique that allows kernel Use After Free (UAF) or Double free vulnerabilities to swap a credential or file structure on the kernel he[…]
How Fast Can You Grep?
Application developers have always had a tricky balance to maintain between speed and security, two requirements that may often feel at odds with each other. Practices that increase speed also pressur[…]
Welcome to the Adversary Universe Podcast: Unmasking the Threat Actors Targeting Your Organization
Cloud-based services are augmenting business operations and being adopted at a record pace. In fact, Gartner® estimates “more than 85% of organizations will embrace a cloud-first principle by 2025 and[…]
CrowdStrike Announces Expanded Partnership at AWS re:Invent 2021
For two days in July, Boston will be the epicenter of innovation in the world of cloud security — and we’re excited to see you there in person! As a proud sponsor of AWS re:Inforce 2022 (July 26-27), […]
Top Threats You Need to Know to Defend Your Cloud Environment
The CrowdStrike eBook, “Protectors of the Cloud: Combating the Rise in Threats to Cloud Environments," reveals how adversaries target and infiltrate cloud environments and recommends best practices fo[…]
How CrowdStrike Detects Cloud Storage Misconfigurations to Protect Valuable Data
The software supply chain remains a weak link for an attacker to exploit and gain access to an organization. According to a report in 2021, supply chain attacks increased by 650%, and some of the atta[…]
CrowdStrike Announces $200 Million Series E Financing Round with New and Existing Investors
As organizations increasingly move to hybrid cloud environments to increase agility, scale and competitive advantage, adversaries are correspondingly looking to exploit these environments. According t[…]
Compromised Docker Honeypots Used for Pro-Ukrainian DoS Attack
Container and cloud-based resources are being abused to deploy disruptive tools. The use of compromised infrastructure has far-reaching consequences for organizations who may unwittingly be participat[…]
CrowdStrike Delivers Adversary-Focused, Platform Approach to CNAPP and Cloud Security
CrowdStrike Falcon® delivers comprehensive cloud security, combining agent-based and agentless protection in a single, unified platform experience Integrated threat intelligence delivers a powerful, a[…]
Leading Global Brands Secure Themselves with CrowdStrike
LemonDuck, a well-known cryptomining botnet, is targeting Docker to mine cryptocurrency on Linux systems. This campaign is currently active. It runs an anonymous mining operation by the use of proxy p[…]
Maintaining Security Consistency from Endpoint to Workload and Everywhere in Between
In today’s fast-paced world, mobility, connectivity and data access are essential. As organizations grow and add more workloads, containers, distributed endpoints and different security solutions to p[…]
Forrester Names CrowdStrike a Leader in the 2021 Wave for External Threat Intelligence
“In its current CWS offering, the vendor has great CSPM capabilities for Azure, including detecting overprivileged admins and enforcing storage least privilege and encryption, virtual machine, and net[…]
Malspam in the Time of COVID-19
CrowdStrike cloud security researchers discovered a new vulnerability (dubbed “cr8escape” and tracked as CVE-2022-0811) in the Kubernetes container engine CRI-O. CrowdStrike disclosed the vulnerabilit[…]
The Easy Solution for Stopping Modern Attacks
Modern cyberattacks are multifaceted, leveraging different tools and techniques and targeting multiple entry points. As noted in the CrowdStrike 2022 Global Threat Report, 62% of modern attacks do not[…]
Why Machine Learning Is a Critical Defense Against Malware
Migrating to the cloud has allowed many organizations to reduce costs, innovate faster and deliver business results more effectively. However, as businesses expand their cloud investments, they must a[…]
How to Protect Cloud Workloads from Zero-day Vulnerabilities
Protecting cloud workloads from zero-day vulnerabilities like Log4Shell is a challenge that every organization faces. When a cloud vulnerability is published, organizations can try to identify impacte[…]
Know Your Enemy: Exploiting the Dell BIOS Driver Vulnerability to Defend Against It
On Jan. 18, 2022, researchers found a heap base buffer overflow flaw (CVE-2022-0185) in the Linux kernel (5.1-rc1+) function “legacy_parse_param” of filesystem context functionality, which allows an o[…]
New CrowdStrike Capabilities Simplify Hybrid Cloud Security
Cryptocurrency mining has become very popular among malicious actors that aim to profit by exploiting cloud attack surfaces. Exposed Docker APIs have become a common target for cryptominers to mine va[…]
Why You Need an Adversary-focused Approach to Stop Cloud Breaches
It should come as little surprise that when enterprise and IT leaders turned their attention to the cloud, so did attackers. Unfortunately, the security capabilities of enterprises have not always kep[…]
5 Common Hybrid IT Security Challenges and How to Overcome Them
Digital transformation has pushed organizations to adopt a hybrid IT approach and has created a mix of on-premises and cloud infrastructure that has to be supported and protected. Unfortunately, while[…]
4 Major Falcon LogScale Next-Gen SIEM Updates That Accelerate Time-to-Insights
Security budgets are not infinite. Every dollar spent must produce a return on investment (ROI) in the form of better detection or prevention. Getting the highest ROI for security purchases is a key c[…]
RSAC 2022: CrowdStrike Innovations that Prioritize Data
We’re ready to meet you in person in Las Vegas! CrowdStrike is a proud Gold sponsor of AWS re:Invent 2021, being held Nov. 29 through Dec. 3. Stop by Booth #152 at the Venetian for a chance to obtain […]
Gimme Shellter
Developing applications quickly has always been the goal of development teams. Traditionally, that often puts them at odds with the need for testing. Developers might code up to the last minute, leavi[…]
macOS Malware Is More Reality Than Myth: Popular Threats and Challenges in Analysis
With virtualization in the data center and further adoption of cloud infrastructure, it’s no wonder why IT, DevOps and security teams grapple with new and evolving security challenges. An increase in […]
Closing the Cloud Security Skills Gap: MDR for the Cloud
The need for speed and agility in today’s digital business requires changes to IT infrastructure, most notably the shift to cloud-native architectures and the adoption of DevOps best practices to impr[…]
CrowdStrike and AWS Expand Partnership to Offer Customers DevOps-Ready Security
Organizations continue to be targeted by sophisticated threats that lead to potential breaches. Customers need the proper people, process, intelligence and technology to be able to reduce risk and sto[…]
Detect Adversary Behavior in Real Time With CrowdStrike Falcon® Horizon and Amazon EventBridge
By integrating Amazon EventBridge with CrowdStrike Falcon® Horizon™ cloud security posture management, CrowdStrike has developed a cloud-based solution that allows you to detect threats in real time. […]
Stop Cloud Breaches With Threat Graph Cloud-Powered Analytics: Intelligent, Automated, Accurate
Drawing benefits from CrowdStrike’s network effect requires handling large amounts of data — volumes and volumes of it. In fact, CrowdStrike stores more than 15 petabytes of data in the cloud that it […]
The Myth of Part-time Hunting, Part 1: The Race Against Ever-diminishing Breakout Times
The term “threat hunting” is increasingly thrown around the cybersecurity industry as a catch-all for any proactive or human-lead defensive security measures. This is evidenced by the SANS 2020 Threat[…]
Three Key Features of Log Management for Cloud Native Systems
This blog was originally published Nov. 16, 2020 on humio.com. Humio is a CrowdStrike Company. Using log management to provide a vital record of operations and proactively detect performance and secur[…]
Google Capital Bets Big on CrowdStrike to Accelerate Hyper-growth
Organizations adopting cloud-native applications face an increasingly diverse and sophisticated threat landscape, in addition to proliferating devices and expanding remote workforces. Meeting these ch[…]
Evaluating Your Organization's Security Approach: Tips For BOD and C-Level Execs
Containers provide a wide range of benefits to both developers and system administrators — increased agility, flexibility and scalability among them. With the increase in adoption, containers have als[…]
How to Fill the Cybersecurity Skills Gap With Homegrown Talent
Compromises of cloud accounts have been a hot topic in the security industry lately, but the common themes we are seeing, such as compute-resource cryptomining and storage bucket data theft, are not t[…]
Do You Know What’s Hiding in Your Containers?
Between the growth of cloud-native applications and the demands of faster application delivery, the use of containers is widely predicted to continue to increase. In fact, a recent study conducted by […]
To Get Cloud Security Cooking, You Need The Right Recipe For Success
Slow down a development team with security, and expect to be greeted with a wave of frustration. Between a lack of integration of security tools and confusion about shared responsibility, security tea[…]
Falcon OverWatch Hunts Down Adversaries Where They Hide
The need for speed and agility in today’s digital business requires changes to IT infrastructure, most notably the shift to cloud-native architectures and the adoption of DevOps. This shift has led ma[…]
Solving the Complexity of Azure Identity: Horizon Identity Analyzer
There are a lot of complexities when managing identity in Microsoft Azure, primarily in gaining end-to-end visibility of what a user can do and what properties are applied to them to handle their acce[…]
First-Ever Adversary Ranking in 2019 Global Threat Report Highlights the Importance of Speed
Many industry analysts project that infrastructure as a service (IaaS) will continue to grow as companies seek ways to slash costs and increase business resilience and agility. While it carries the pr[…]
CrowdStrike Debuts Product and Partnership News at AWS re:Invent 2019
CrowdStrike is proud to be a Gold Sponsor of AWS re:Invent 2020, the world’s largest and most comprehensive cloud computing and cloud learning event, happening now — November 30 to December 18, 2020. […]
CrowdStrike Falcon® Forensics: Ditch Inefficient Incident Response Tools for Good
One of the biggest challenges of the cloud today is properly configuring resources to prevent breaches. Various breaches have proven this, such as the LA Times breach in 2018, where an S3 bucket was m[…]
Blind Spots in the Cloud
Visibility in the cloud is an important but difficult problem to tackle. It differs among cloud providers, and each one has its own positives and negatives. This blog reviews some of the logging and v[…]
CrowdStrike Mobile Threat Report Offers Trends and Recommendations for Securing Your Organization
Built in the cloud and for the cloud, cloud-native applications are driving digital transformation and creating new opportunities to increase efficiency. Taking a cloud-native approach brings both spe[…]
Intelligence-led Rapid Recovery: Getting Back to Business Faster
The adoption of the cloud has fundamentally changed the game when it comes to how businesses go to market and develop modern applications. Today’s application lifecycle places a premium on speed to ma[…]
Adversaries Go Hands-On in Japan: Know the Threat and Know the Solution
CrowdStrike® is thrilled to be attending AWS re:Invent 2019 this week as an AWS Partner Network (APN) sponsor. Amazon Web Services’ annual conference in Las Vegas draws cloud computing professionals f[…]
Confessions of a Responder: The Hardest Part of Incident Response Investigations
It’s not the disk forensics. It’s not the log analysis. It’s not even the lawyers (we love working with law firms!). It’s the lack of an effective technology deployment strategy. CrowdStrike® Services[…]
Uncovering The “Unknown Unknowns”: Why Threat Hunting is a Security Must-Have
If you’re living off the land, there are a few different methods you can use to survive, such as setting traps or finding edible plants. However, some animals are too smart to get caught and some plan[…]
CrowdStrike Falcon® Detects Kernel Attacks Exploiting Vulnerable Dell Driver (CVE-2021-21551)
CrowdStrike® is thrilled to introduce Falcon Discover™ for AWS, a new solution that delivers our next-generation IT cloud hygiene features across AWS workloads, ensuring advanced visibility into AWS E[…]
Stopping Cyber “Shakedowns” — How to Protect Against Extortion-Based eCrime
Internet extortion and “datanapping” have become common occurrences, with increasingly high-profile victims ranging from hospitals to Hollywood studios. A new webcast explores the growth in stealthy e[…]
Unexpected Adventures in JSON Marshaling
Event Stream Processing (ESP) has been a central component of CrowdStrike Falcon®’s IOA approach since CrowdStrike's inception. In this post we'll take a closer look at ESP — along with its utility an[…]
Cloud-based Security: Future of the Industry?
Alex Stamos, formerly with Yahoo and now CSO at Facebook, gave a really interesting talk at AppSec California 2015 recently titled "AppSec is Eating Security." Among the many insightful comments he ma[…]



![Qatar’s Commercial Bank Chooses CrowdStrike Falcon®: A Partnership Based on Trust [VIDEO]](https://assets.crowdstrike.com/is/image/crowdstrikeincstage/Edward-Gonam-Qatar-Blog2-1)