editorialteam
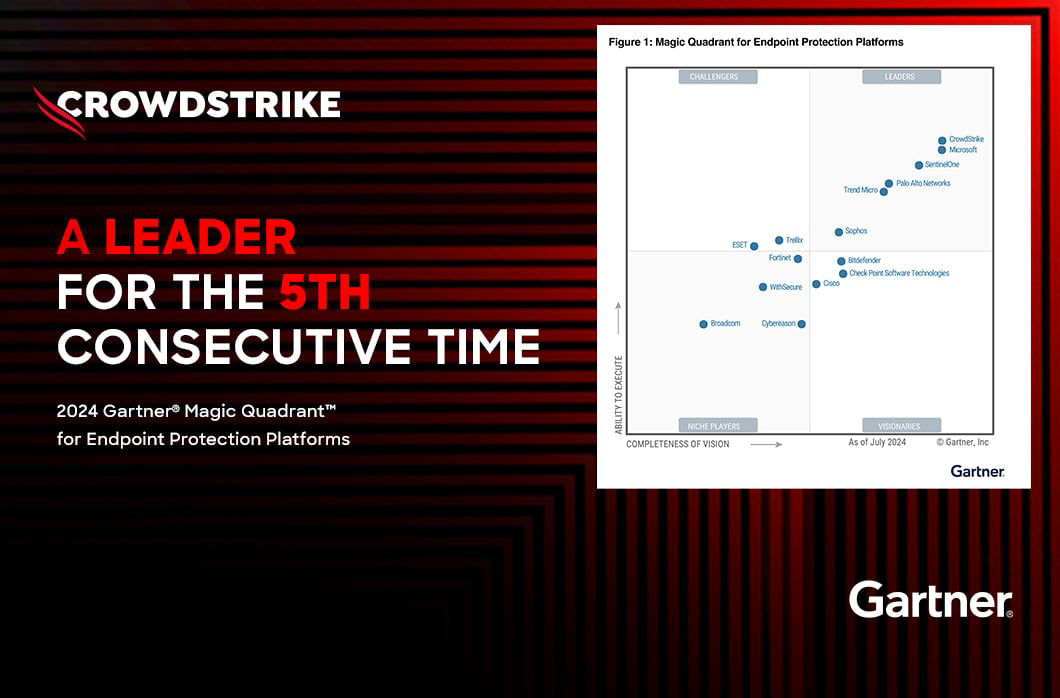
Our Customers Have Spoken: CrowdStrike Delivers the Best in EDR, EPP and XDR
Time and again, analyst reports, independent tests and numerous other awards and acknowledgements affirm CrowdStrike is a leader in cybersecurity. Why is this important? Because when CrowdStrike is #1[…]
Why Your Small Business Needs to Rethink Its Cybersecurity Strategy
Cybercrime is a big problem for small businesses, and the risk of advanced threats continues to grow. This Cybersecurity Awareness Month, learn how to protect your SMB or nonprofit from attacks that t[…]
Threat Actor Uses Fake CrowdStrike Recovery Manual to Deliver Unidentified Stealer
The countdown continues! As Fal.Con 2022 quickly approaches, we’re excited to share more information about the security industry visionaries and notable talks on the agenda for the sixth annual CrowdS[…]
Could you be a threat hunter? Humio and Corelight make it easy for customers to get started with threat hunting
The countdown has begun! In less than a month, we’ll gather in Las Vegas for Fal.Con 2022, the sixth annual CrowdStrike cybersecurity conference. We’re excited to bring you an event packed with produc[…]
Mergers and Acquisitions: Cybersecurity Due Diligence
CrowdStrike last week announced Michael Rogers was promoted to vice president of global business development, channel and alliances. His appointment comes after years of driving growth in CrowdStrike’[…]
CrowdStrike CEO: Pandemic Fuels Digital and Security Transformation Trends
Since we founded CrowdStrike, we’ve paved the way as one of the most prominent remote-first companies. We’ve planted roots in communities around the world — from Sunnyvale to London and from Pune to T[…]
On-Demand Webcast Discusses “Making 60-Minute Remediation a Reality”
This is the first blog post in our four-part series for 2021 Cybersecurity Awareness Month. Read Part 2 | Part 3 | Part 4. Cybersecurity Awareness Month's Week 1 theme of “Be Cyber Smart” presents a g[…]
CrowdStrike CTO Michael Sentonas Shares Insights on Humio
How do events such as the past year’s global pandemic, outcries for social justice and tumultuous elections affect cybersecurity? “These sorts of global events are the perfect storm for adversaries,” […]
CrowdStrike CEO Joins Power Panel Discussion with Zoom and Slack CEOs
Three business leaders whose companies have been technologically front and center since the outset of the global pandemic convened a “CEO Power Panel” at our Fal.Con 2020 cybersecurity conference. “If[…]
CrowdStrike’s work with the Democratic National Committee: Setting the record straight
June 5, 2020 UPDATE Blog update following the release of the testimony by Shawn Henry, CSO and President of CrowdStrike Services, before the House Intelligence Committee that was recently declassified[…]
How Malicious Insiders Use Known Vulnerabilities Against Their Organizations
A recent article in CSO Australia by David Braue is titled “Businesses Risk Becoming “Collateral Damage” in Nation-State Cyber Wars.” The author interviewed CrowdStrike CSO Shawn Henry on why organiza[…]
Danger Close: Fancy Bear Tracking of Ukrainian Field Artillery Units
A recent article on Dark Reading by CrowdStrike VP of Intelligence Adam Meyers is titled “The Big E-Crime Pivot.” It puts forth the argument that cybercriminals “have begun to recognize that enterpris[…]
Who is FANCY BEAR (APT28)?
The nation-state adversary group known as FANCY BEAR (also known as APT28 or Sofacy) has been operating since at least 2008 and represents a constant threat to a wide variety of organizations around t[…]
CrowdStrike Becomes a Publicly Traded Company
CrowdStrike® added a prestigious award to its many achievements when CEO and co-founder, George Kurtz, was named Ernst & Young (EY) Entrepreneur of the Year in the security category for Northern Calif[…]
Critical Vulnerability in CredSSP Allows Remote Code Execution on Servers Through MS-RDP
Benjamin Franklin wisely stated that, “An ounce of prevention is worth a pound of cure.” In keeping with this timeless principle, one can’t help wondering what is required to provide appropriate preve[…]
CrowdStrike Falcon® and Humio: Leverage All Your FDR Data in One Place
We started CrowdStrike five years ago with the mission to revolutionize endpoint security. At that time, no one was talking about replacing legacy and bloated AV agents with a next-generation, cloud-d[…]
The Three Steps of Proactive Threat Hunting
Security teams in the private and public sector are increasingly recognizing the need to actively “hunt” for threats targeting their organizations. Larger, well resourced organizations may have the ab[…]
CrowdStrike evaluated in Gartner’s Comparison of Endpoint Detection and Response Technologies and Solutions
Leading analyst firm Gartner has recently published a comparative assessment called Comparison of Endpoint Detection and Response Technologies and Solutions*. This is the first direct competitive anal[…]
Improve Threat Hunting with Long-Term, Cost-Effective Data Retention
According to a recent Harvard Business Review report, 84 percent of enterprises have increased their Cloud usage in the past year. Fueling this major business migration to the Cloud are the well-docum[…]
Brian Kelly, CSO of Rackspace, Shares Why He Chose CrowdStrike
When you’re in charge of protecting not only your company’s critical business information, but also that of your company’s customers, there’s no option for a security breach. Brian Kelly, Chief Securi[…]
Cloud-based Security: Future of the Industry?
Alex Stamos, formerly with Yahoo and now CSO at Facebook, gave a really interesting talk at AppSec California 2015 recently titled "AppSec is Eating Security." Among the many insightful comments he ma[…]
VENOM Vulnerability Details
Recently, I discovered a vulnerability in QEMU's virtual Floppy Disk Controller (FDC), exploitation of which may allow malicious code inside a virtual machine guest to perform arbitrary code execution[…]
VENOM Vulnerability: Community Patching and Mitigation Update
Today, CrowdStrike disclosed a critical virtual machine escape vulnerability (which we named VENOM) discovered by our Senior Security Researcher Jason Geffner. VENOM affects a number of open-source hy[…]
Healthcare Is Experiencing a Cybersecurity Emergency
April is an unbelievably busy month for IT security professionals. In addition to daily online combat with bears, kittens, pandas, and other adversaries, this month is full of security conferences. Fr[…]
Adapting Cyber Security in a New Era of Corporate Destruction
Corporations suffered more cyber attacks in 2014 than ever before, causing the loss of business intelligence and personally identifiable information at an alarming rate. As a result, confidentiality i[…]
The Battle for Safe Networks Could End with Open Sharing of Information
In our last post, Shawn Henry, president of CrowdStrike Services and sought-after cybersecurity expert, talked with us about cybersecurity trends in 2014 and 2015. In this installment of that conversa[…]
Cyber Skirmish: Russia v. Turkey
The Adversary Manifesto recently spoke with Shawn Henry, President of CrowdStrike Services about geopolitics and cybersecurity. Henry is a sought-after expert on cybersecurity who was formerly the exe[…]
The Adversary Manifesto: A Q&A with CrowdStrike’s VP of Threat Intelligence
Adam Meyers runs CrowdStrike's Global Threat Intelligence team and is responsible for creating actionable intelligence that enables customers to understand the who, what, and why of a targeted attack.[…]
Naming Adversaries and Why It Matters to Your Security Team
At CrowdStrike, we’ve seen a moderate increase in Java-based malware recently, with Remote Access Tools (RATs) like Adwind becoming increasingly prevalent. Reverse engineering Java is typically very s[…]
Analysis of a CVE-2013-3906 Exploit
Many of CrowdStrike’s customers are often targeted by email phishing campaigns and strategic web compromises (also known as watering-hole attacks). These attacks use exploits to take advantage of vuln[…]
Unpacking Dynamically Allocated Code
Background Today, most malware is obfuscated to make it more difficult for traditional antivirus engines to detect the malicious code and to make it more arduous for analysts to understand the malware[…]



![Qatar’s Commercial Bank Chooses CrowdStrike Falcon®: A Partnership Based on Trust [VIDEO]](https://assets.crowdstrike.com/is/image/crowdstrikeincstage/Edward-Gonam-Qatar-Blog2-1)