Manoj Ahuje
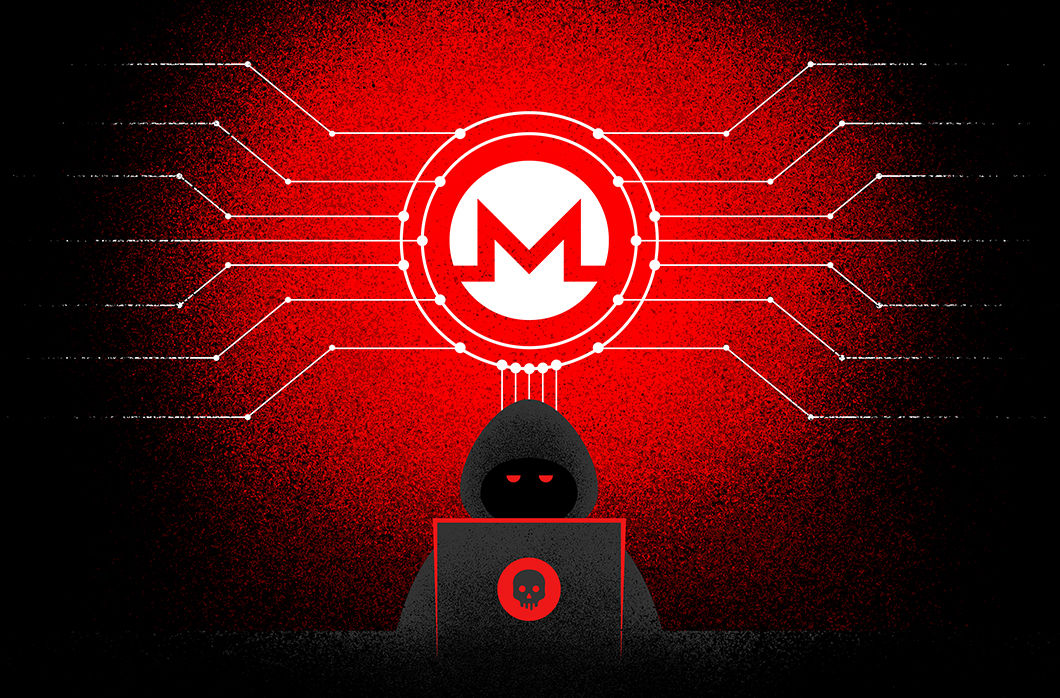
CrowdStrike Discovers First-Ever Dero Cryptojacking Campaign Targeting Kubernetes
Two new privilege escalation CVEs, CVE-2023-2640 and CVE-2023-32629, have been discovered in the Ubuntu kernel OverlayFS module. The CVEs affect not only any Ubuntu hosts running with vulnerable kerne[…]
CrowdStrike Integrated Intelligence and Deployment Automation Enhance New AWS Network Firewall
CrowdStrike has uncovered a new cryptojacking campaign targeting vulnerable Docker and Kubernetes infrastructure using an obscure domain from the payload, container escape attempt and anonymized “dog”[…]
DirtyCred: Opening Pandora’s Box to Current and Future Container Escapes
What Is DirtyCred? DirtyCred is a new Linux kernel exploitation technique that allows kernel Use After Free (UAF) or Double free vulnerabilities to swap a credential or file structure on the kernel he[…]
How CrowdStrike Detects Cloud Storage Misconfigurations to Protect Valuable Data
The software supply chain remains a weak link for an attacker to exploit and gain access to an organization. According to a report in 2021, supply chain attacks increased by 650%, and some of the atta[…]
CVE-2022-23648: Kubernetes Container Escape Using Containerd CRI Plugin and Mitigation
CVE-2022-23648, reported by Google’s Project Zero in November 2021, is a Kubernetes runtime vulnerability found in Containerd, a popular Kubernetes runtime. It lies in Containerd’s CRI plugin that han[…]
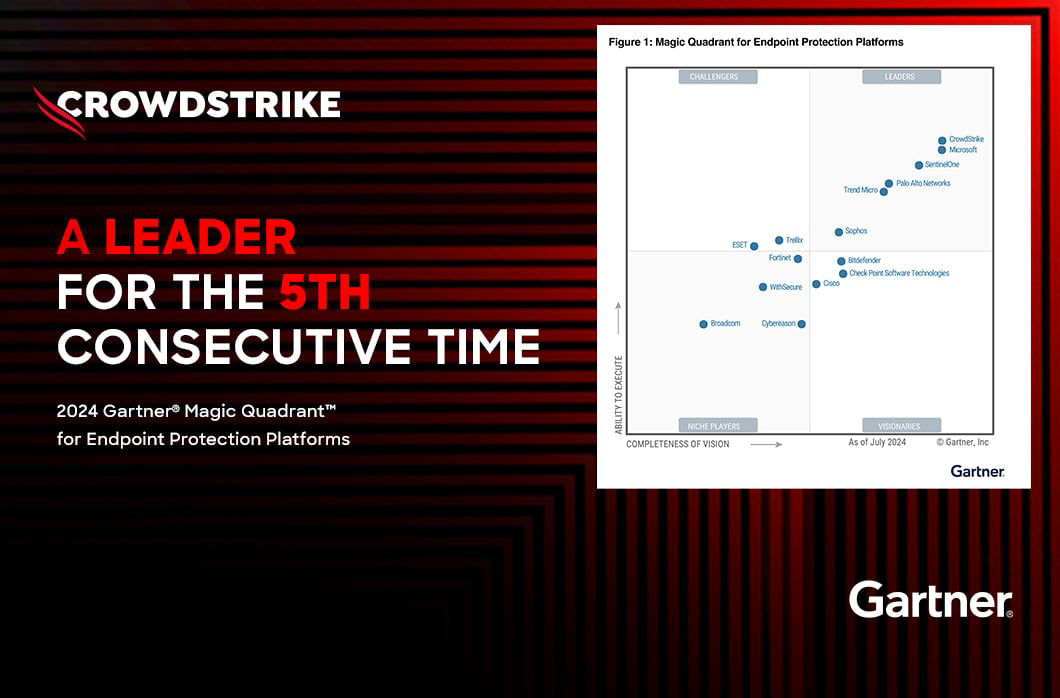
Leading Global Brands Secure Themselves with CrowdStrike
LemonDuck, a well-known cryptomining botnet, is targeting Docker to mine cryptocurrency on Linux systems. This campaign is currently active. It runs an anonymous mining operation by the use of proxy p[…]
Know Your Enemy: Exploiting the Dell BIOS Driver Vulnerability to Defend Against It
On Jan. 18, 2022, researchers found a heap base buffer overflow flaw (CVE-2022-0185) in the Linux kernel (5.1-rc1+) function “legacy_parse_param” of filesystem context functionality, which allows an o[…]
New CrowdStrike Capabilities Simplify Hybrid Cloud Security
Cryptocurrency mining has become very popular among malicious actors that aim to profit by exploiting cloud attack surfaces. Exposed Docker APIs have become a common target for cryptominers to mine va[…]



![Qatar’s Commercial Bank Chooses CrowdStrike Falcon®: A Partnership Based on Trust [VIDEO]](https://assets.crowdstrike.com/is/image/crowdstrikeincstage/Edward-Gonam-Qatar-Blog2-1)