shawnh
eCriminals Share Ways to Impersonate School Staff to Steal Paychecks
Cyber threats to elections in the U.S. and abroad remain at an elevated level and continue to evolve. It’s appropriate and encouraging to see continued growth and investment in cybersecurity efforts w[…]
CVE-2024-3094 and the XZ Upstream Supply Chain Attack: What You Need to Know
The CrowdStrike Services team has issued its latest report: “CrowdStrike Services Cyber Front Lines Report: Observations From the Front Lines of Incident Response and Proactive Services in 2020 and In[…]
Securing Elections Globally: How CrowdStrike Is Helping
As a global leader in protecting elections, we want to explain our perspective on election security issues and share some resources with the elections community. Free and fair elections are the corner[…]
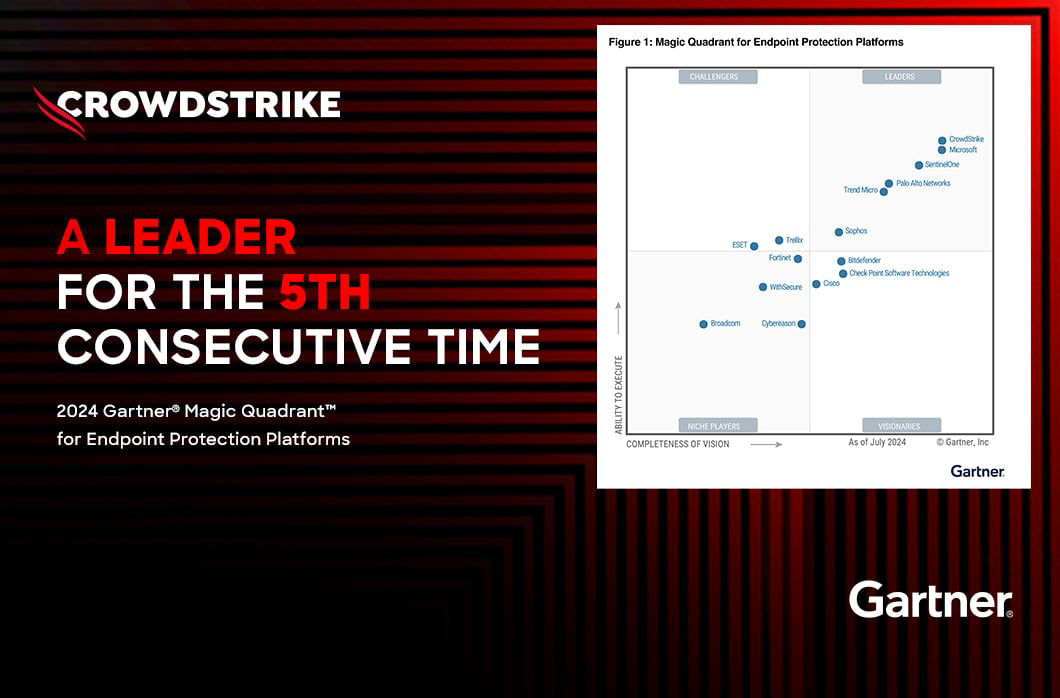
CrowdStrike Named a Leader in the 2019 Forrester Wave for Endpoint Security Suites
"CrowdStrike is a global company built on three pillars: threat intelligence, endpoint protection, and incident response. Each of these capabilities not only informs the others but is buttressed by co[…]
Forrester Names CrowdStrike a Leader in the 2018 Wave for Endpoint Detection And Response
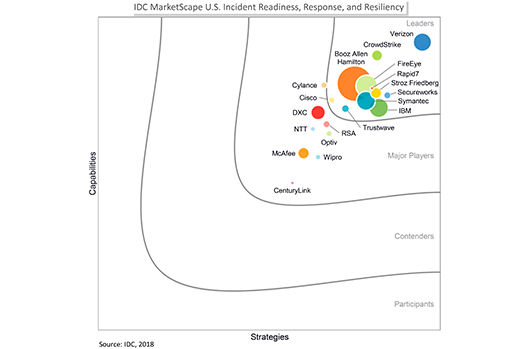
I am proud to announce that CrowdStrike® is positioned as a leader in the IDC MarketScape: U.S. Incident Readiness, Response, and Resiliency 2018 Vendor Assessment – Beyond the Big 5 Consultancies (do[…]
Why Cybersecurity Should be a Board-Level Discussion
The idea that cybersecurity is a board-level concern is not new. Private sector companies and their computer networks have been the target of cyberattacks for decades. This is because they generate th[…]
Operators of SamSam Continue to Receive Significant Ransom Payments
On March 22, the city of Atlanta, Georgia, was crippled by a ransomware attack that has since been identified as a SamSam (aka Samas and SamSa) ransomware variant — the work of a threat actor tracked […]
Meet the Protectors: New Video Series Spotlights Cybersecurity Leaders Powered by CrowdStrike
Given today’s global cyber threatscape, the increased amount of targeted attacks against the financial sector — and New York City’s position as the financial capital of the U.S. (though some would arg[…]
Mimikatz in the Wild: Bypassing Signature-Based Detections Using the “AK47 of Cyber”
November 2016 has been proclaimed Critical Infrastructure Security and Resilience Month. This is an annual effort, beginning this year, to educate and engage citizens about the vital role critical inf[…]
M&A – Buying While Cyber Blind?
The year 2015 marked the highest ever value of mergers & acquisitions with an astounding $4.6 trillion. If 2016 follows this trajectory, we’re looking at over 18,000 M&A events to occur this year, man[…]
Top 5 Cybersecurity Mistakes Companies Make and How to Avoid Them
Cybersecurity requires a holistic organizational approach. From the leadership to each rank-and-file employee, a concerted effort must be maintained to establish, execute and follow-through with a pla[…]



![Qatar’s Commercial Bank Chooses CrowdStrike Falcon®: A Partnership Based on Trust [VIDEO]](https://assets.crowdstrike.com/is/image/crowdstrikeincstage/Edward-Gonam-Qatar-Blog2-1)