CROWDSTRIKE FALCON®
ELITE ADVANCED BREACH PROTECTION
Take breach-stopping power to the next level with integrated endpoint and identity protection, expanded visibility, and elite threat-hunting.
Contact sales-
Falcon
PreventNext-generation
antivirus -
Falcon
Device ControlUSB device control
-
Falcon Firewall
ManagementHost firewall control
-
Falcon
Adversary OverWatchThreat hunting and intelligence
-
Falcon
Insight XDRDetection & response
-
Falcon
DiscoverIT hygiene
-
Falcon Identity
ProtectionIdentity protection
-
CROWDSTRIKE
SERVICESExpress support
- Falcon Elite
Full endpoint and identity protection with threat hunting and expanded visibility
Flexible Bundles:
Included Component
Add-on
REAP THE BENEFITS OF CROWDSTRIKE’S
FALCON ELITE:
ADVANCED BREACH PROTECTION
Falcon Elite is the industry’s only unified solution combining next-gen AV (NGAV) and endpoint detection and response (EDR), with real time identity protection, elite threat hunting and IT hygiene.
→
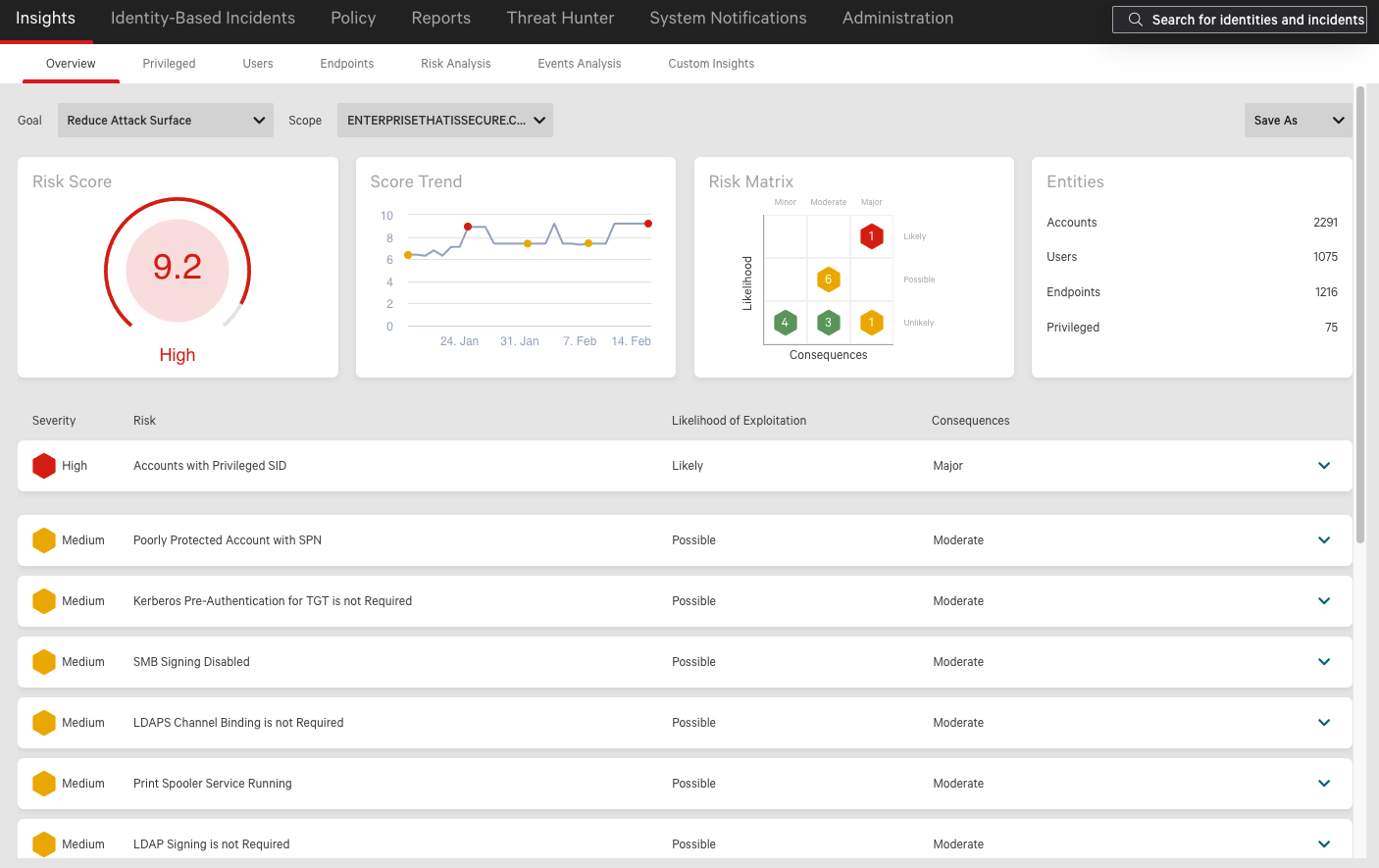
Reduce the attack surface and get hyper-accurate detection of identity-based threats, extending MITRE ATT&CK® coverage.
Stop modern attacks like ransomware that use stolen credentials even when adversaries manage to get past an unprotected endpoint.
Extend MFA protection to legacy applications and protocols often exploited by adversaries.
→
-
Falcon Elite is the industry’s only unified endpoint security solution combining next-generation AV, EDR, managed threat hunting, real time identity protection, integrated threat intelligence, and IT hygiene.

→
-
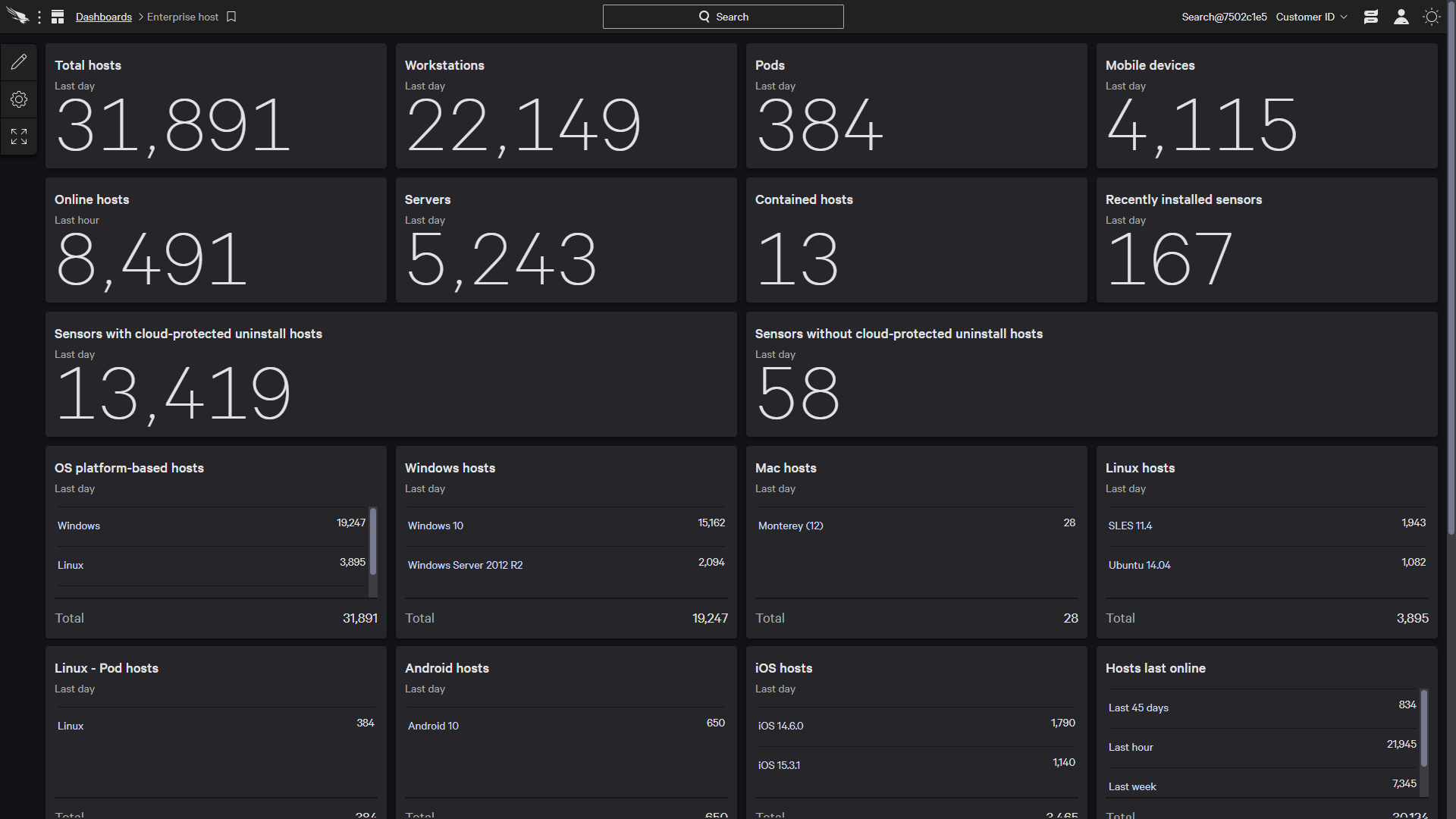
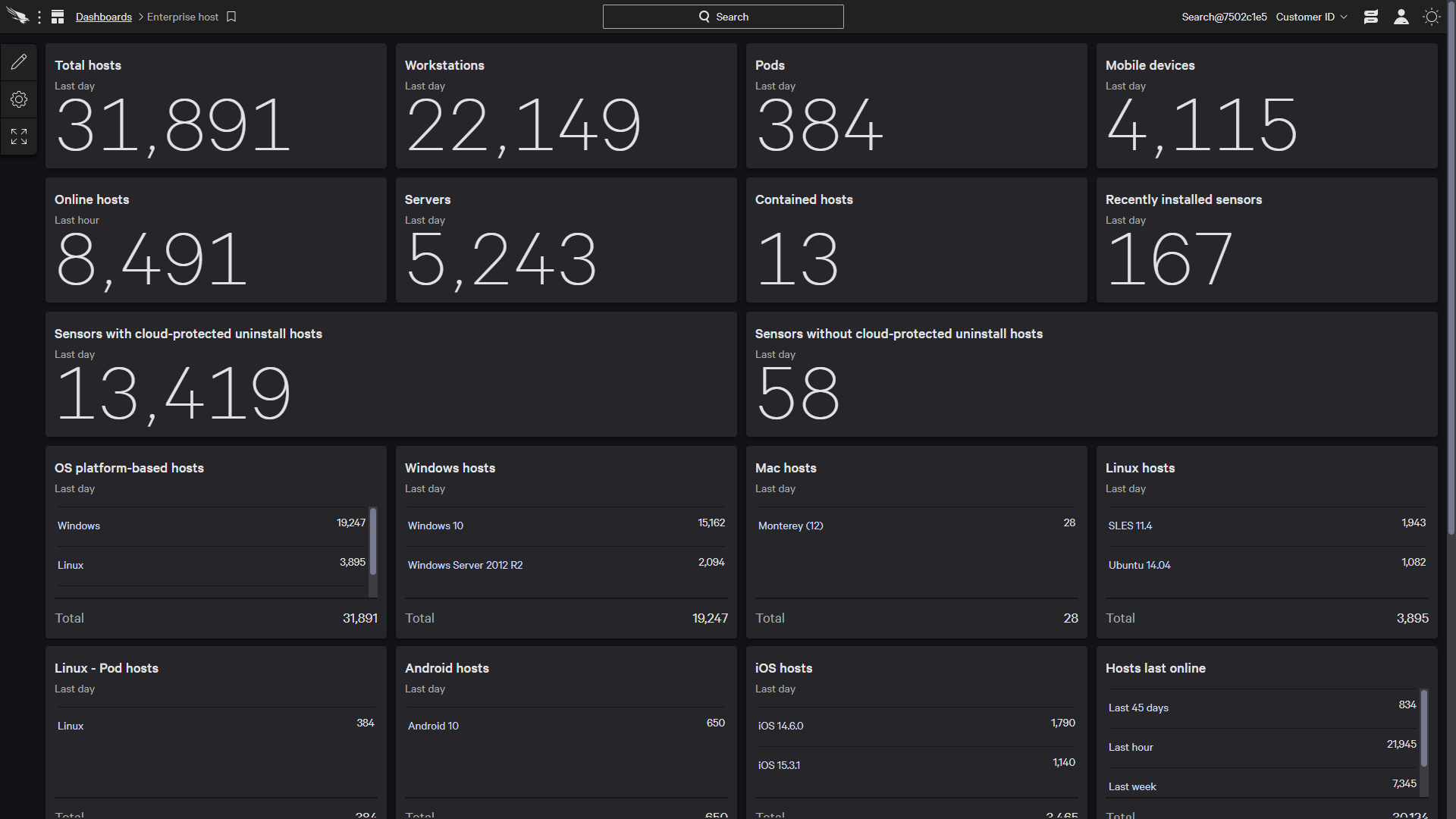
Prepare before an attack occurs by adding the visibility you need to reveal areas of exposure — it identifies unprotected and rogue systems and monitors what applications and user accounts are being used in your environment
Validate your readiness with health checks, proactive configuration and quarterly briefings, and security recommendations from CrowdStrike security experts
operational in hours
→
Includes all the components needed to anticipate, prevent, detect and respond to breaches
Deploys in minutes and is immediately operational
Virtually zero impact on endpoints
Easy upgrade from an existing CrowdStrike solution and add capabilities delivered by the CrowdStrike Falcon® Platform without requiring any deployment
Automatically keeps up to date with SaaS delivery
Adapts to all needs, growth and security status-
Integrated Falcon Fusion orchestrates and automates complex and repetitive tasks — from notifications to response workflows
BUSINESS VALUE
-
Reduces operational
costs -
Reduces endpoint
costs -
Reduces
risks -
Improves endpoint performance
MODULES INCLUDE

←
Hyper-accurate detections and real time protection against identity-driven attacks
Provides immediate visibility across a complex, hybrid identity landscape
Auto-classifies every type of identity — human and service accounts, on-premise or cloud , regular or privileged users
Detects suspicious lateral movement and anomalous authentication traffic in real time
Provides deep insights into identity-based incidents and enables proactive threat hunting of identity-based threats
Enforces risk-based conditional access policies to block or enforce MFA to prevent identity-attacks in real time

←
Detailed visibility over applications, assets and user accounts
Identifies rogue computers instantly
Sees who and what is on your network at all times
Finds unprotected systems
Sees where and how user accounts are being used, including privileged accounts
Gains real-time and historical inventory of application usage in your environment
←
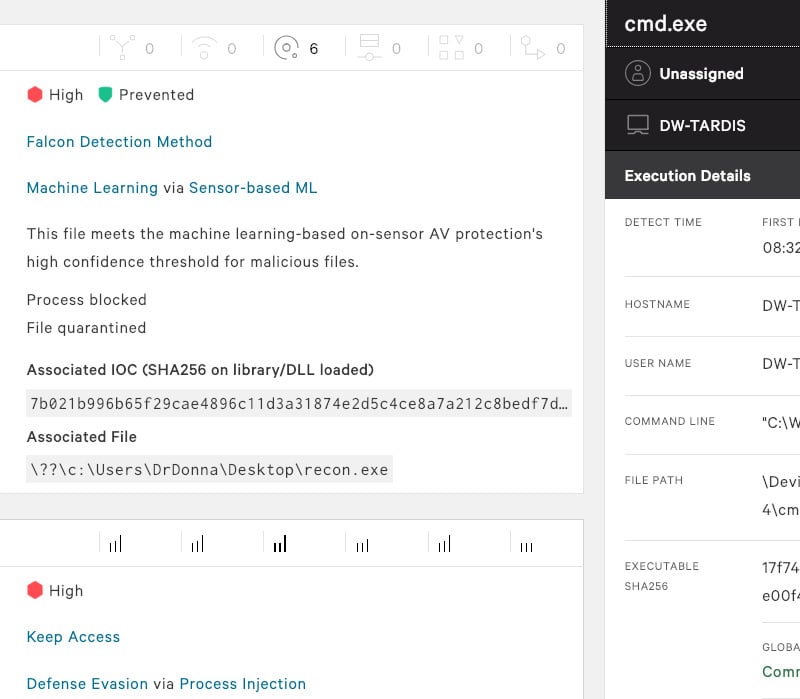
AI powered Machine Learning and IOAs protect against attacks
Protects against known and unknown malware, and malware-free or fileless attacks
Combines the best NGAV prevention technologies such as machine learning, AI-powered indicators of attack (IOAs), high-performance memory scanning and more
Eliminates ransomware
Covers the gaps left by legacy AV-
Fully protects endpoints online and
Cleans up known artifacts left behind from blocked malicious activity

←
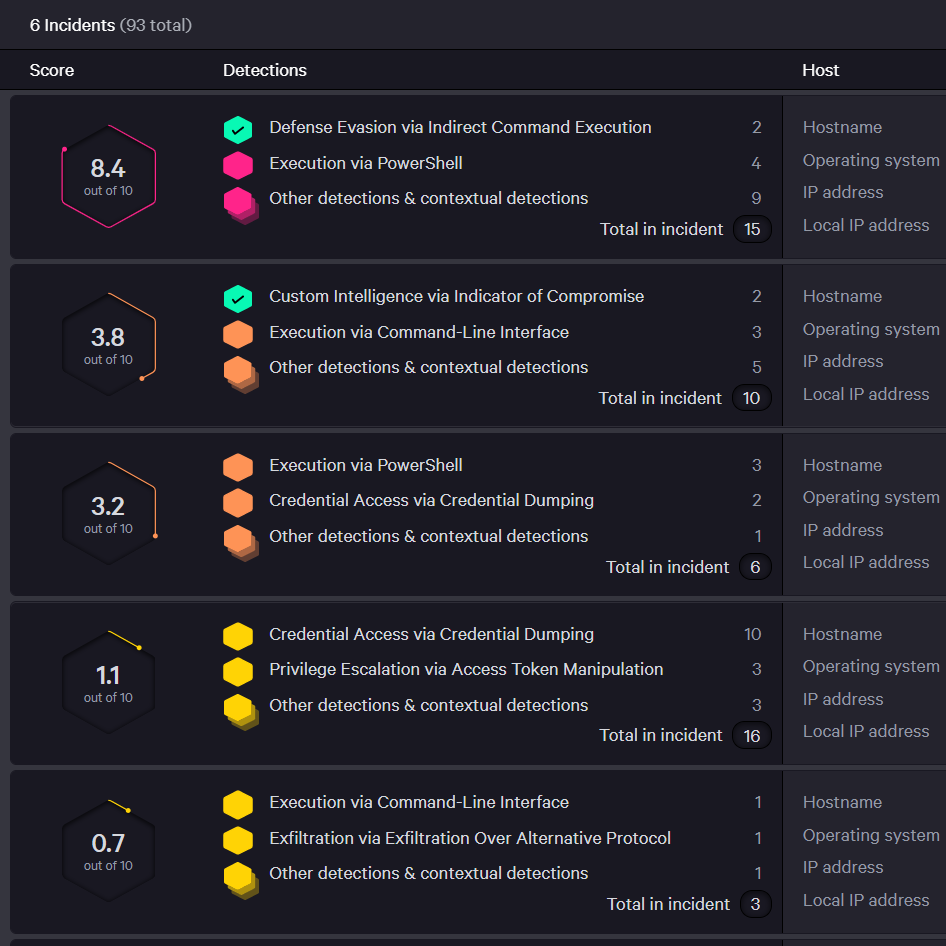
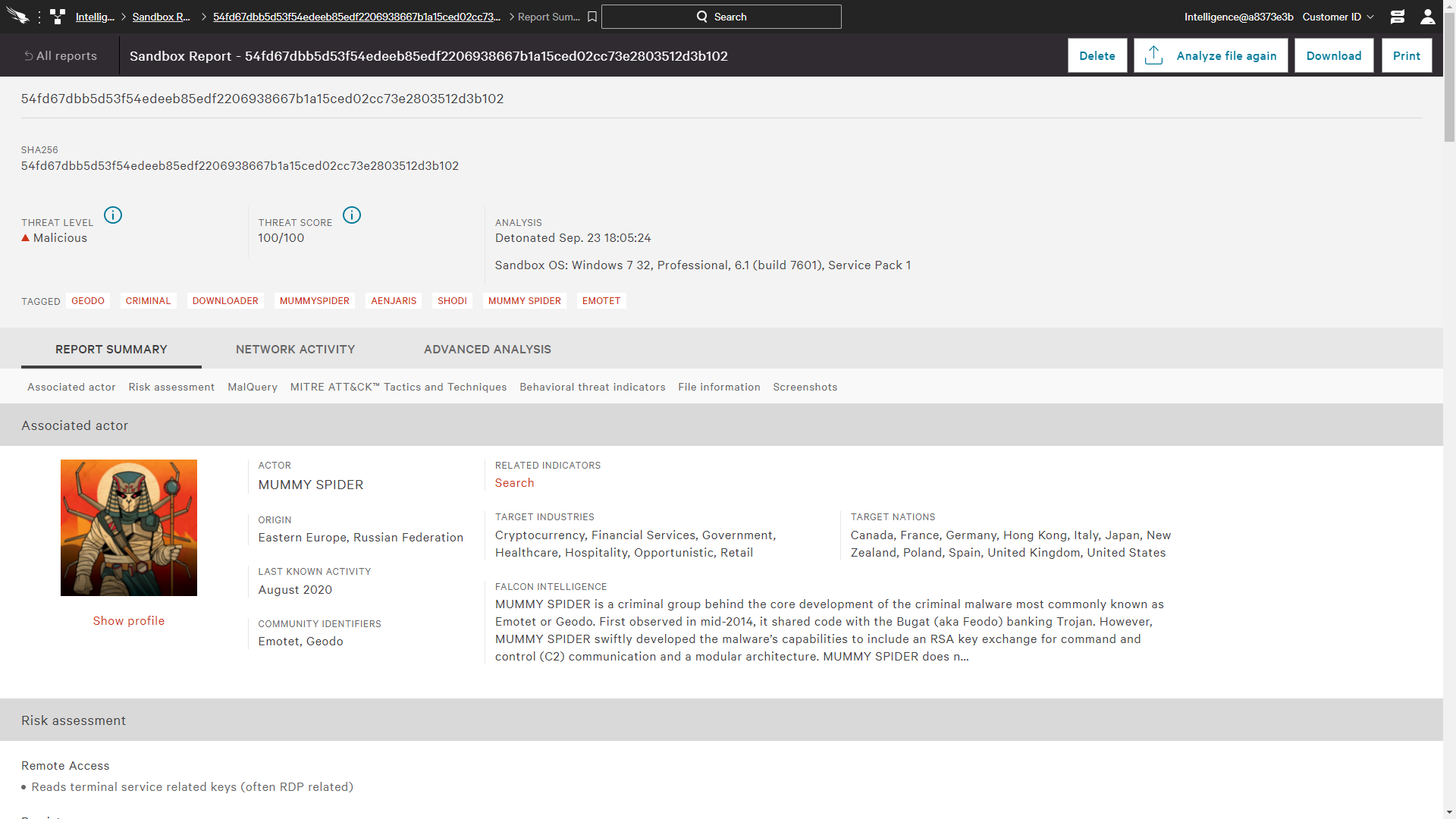
Intelligent EDR automatically detects attacks and threat intel integration provides attribution
Continuous raw event recording provides unparalleled visibility-
Full endpoint activity details enable proactive and managed threat hunting and forensic investigations
-
Intelligent EDR automatically detects and intelligently prioritizes malicious and attacker activity, reducing alert fatigue by 90% or more
Unravels entire attack in the easy-to-use Incident Workbench enriched with context and threat intelligence data
Provides powerful response action to contain and investigate compromised systems, including on-the-fly remote access to endpoints to take immediate action

←
An additional layer of monitoring and analysis to ensure that threats never get missed
Proactively hunts for threats 24/7, eliminating false negatives
Uniquely pinpoints the most urgent threats in your environment and resolves false positives
Threat hunters partner with your security operations team to provide clarity on an attack and guidance on what to do next
←
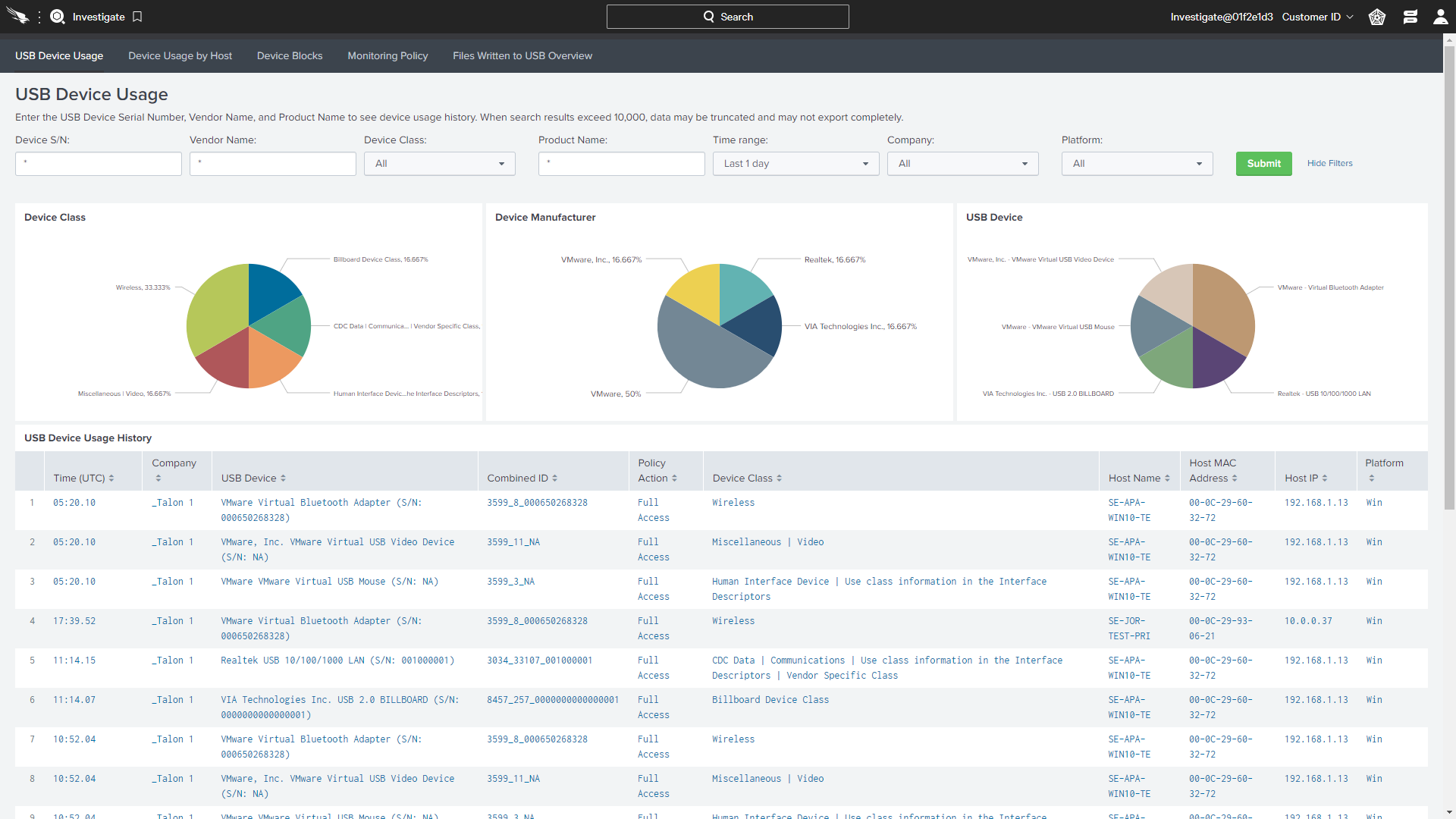
Detailed visibility on USB devices utilization
Granular policy enforcement to ensure control over USB devices used in the environment
Effortless visibility across USB device usage, including what files are being copied to USB storage
Insightful dashboards automatically provide detailed information such as class, vendor, product, serial number

←
Host firewall management made easy
Easily create, enforce and maintain firewall rules and policies
Simplify operations by using the same lightweight Falcon agent, management console and cloud-native architecture
Automatically identify and view specific activities, potential threats and network anomalies
←
Fully understand the threats in your environment and what to do about them
Eliminate guesswork and uncertainty to respond to threats decisively
Automatically determine the scope and impact of threats found in your environment
Easily prioritize responses with threat severity assessment-
Immediately get recovery steps and resolve incidents with in-depth threat analysis
Find out if you are targeted, who is targeting you and how to prepare and get ahead
←
Tens of thousands of endpoints operational in hoursCompare CrowdStrike
See how CrowdStrike’s endpoint security platform stacks up against the competition.
Compare
